The story of a silly misunderstanding, by way of which I significantly improved the efficiency of the MagSpoof (Samy Kamkar‘s famous project).
The MagSpoof
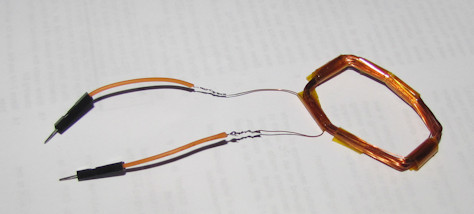
Samy, as you probably know, is a super cool hacker, and among other things, he discovered some weaknesses in American Express credit cards and the way they are issued. About four months ago Samy released a video where he described his findings, and presented the MagSpoof. The MagSpoof is a little proof-of-concept electronic circuit with a copper wire coil, a DC motor driver IC, and an ATtiny85 MCU programmed to match. This device creates an alternating electromagnetic field, carefully timed in a way that fools ordinary magnetic card readers into thinking that a real, physical card is being swiped in them.
I have no intention to counterfeit American Express cards – or any other cards, for that matter – but I was really intrigued by the MagSpoof hardware. So I got a simple MagStripe reader (about $15 from China), collected the components, uploaded Samy’s example code and tried it. It worked. But then I looked into the code itself, and found something that struck me as odd.
Mystery #1
Before we continue, here’s some background. The credit card’s magnetic stripe contains up to three long “bar codes”, made from thin lines of magnetic material with spaces between them. Samy demonstrated this by dipping a card into fine iron powder; the iron stuck to the lines and made them visible. Card readers have sensitive magnetic sensors, which recognize these lines as they pass by when the card is swiped. The MagSpoof replicates the effect of these lines on the sensors by switching the polarity of a strong electromagnetic field nearby.
This scheme obviously worked, but I didn’t understand why. I assumed that the card reader only recognizes the presence or absence of magnetic material (the “bar code” lines), and if that’s the case, what’s the point of changing the polarity? Wouldn’t it be more logical to simply switch the same electromagnetic field on and off?
Mystery #2
After a little experimentation with the code, I was able to show that I was right: the polarity reversal is not required. Turning the field on and off was enough to transmit the same data to the reader, from a similar distance (by rough estimate – I did not measure).

Still, something did not add up. Both in Samy’s original code and in mine, we actually ignored the spaces in the “Bar code”, treating only the lines as triggers to changes in the field. But of course, the spaces do exist, and they contain no magnetic material. The sensors must “see” them when a real card is swiped, so how can the MagSpoof be working without them?
The solution(?)
At that point I learned my big mistake: the lines in the magnetic stripe are not just magnetized – they have specific polarities which alternate between one line and the next. Knowing this, Samy’s code makes much more sense. My code, on the other hand, which does not change the field’s polarity, shouldn’t work at all. But it did!
These mysteries are solved if we assume that the card reader does not care about polarity per se, but about extreme changes in the field; and that it determines what counts as extreme by looking at the field levels detected during the first “sync” bits in the “bar code”.
In this scenario, when you swipe an actual card, or use Samy’s MagSpoof, the card reader identifies the opposite polarities as the extremes, and ignores smaller changes – such as the difference between a line and a space. In other words, the MagSpoof works despite ignoring the spaces, because the card readers themselves ignore the spaces. In my modified MagSpoof, the extremes are different, but the card reader treats them the same, so the spaces are still not required.
Cheap & Efficient
What does it all mean, practically? For a proof-of-concept one-off, like the original MagSpoof, it means nothing; but had I wanted to mass-produce a MagSpoof, my method would have been superior because:
- I have current flowing through the coil in one direction only, so I don’t need the DC motor driver IC – just one little transistor.
- During operation, I turn the field on and off instead of reversing its polarity, so the total power consumption drops in half.
Concluding remarks
I find this story quite interesting, because had I read all the relevant material thoroughly in advance, I wouldn’t have come up with this significant hardware improvement. This is a pretty rare thing to happen – usually, mistakes and misunderstandings only make things worse.
I wrote to Samy about this little discovery. If anyone can confirm (or correct) my assumptions regarding the card reader’s way of working, I’ll be happy to hear.
Until next time…

I made a version of this device accidentally when i was making musical equivilants and decided to use a magsstripe reader to do my scratching. i modified the output of the reader to input to audacity and would just run different cards magstripes back and forth to produce scratching similar to turntables and could even have multiple encodings on different cards. anyhow, audacity’s output was to a set of headphones with really longwire coming from the stereo jack that i plugged into my setup, which to shorten i wrapped and zap stapped into a coil. i noticed that the magstripe reader was not only picking up and reproducing what i had encoded on to various cards and causing something of an echo or hall effect when i unintentially placed the coiled up headphone amplified output in proximity to the magstripe reader i was using to imitate turntables. so i started playing various songs from music i listened to from music artists i listened to that had turntable scratching within the songs looking for im not quite sure what and found that not only the scratching in the songs but also the vocals would be picked up by the magstripe reader and converted to ANSII and piped into audacity producing mostly jarble but sometimes words or phrases would seem to manifest from then song that were not even spoken in the song. if none of what i just said makes no sense then i guess the take away from what i say is that after a bit mor tinkering i ended making a version of magspoofer where i could swipe a credit card convert it to a sound file like an mp3 store it to an sd card put the sd into an mp3 player and when i plugged in a coil to its aux (my headphones with the really long wire which i had wrapped and zapstrapped into a coil) i could play mp3 files of payment cards with adjustments using volume i could put the coil goin to my headphones in proximity to pos terminals and spoof a creditcard from my mp3 player. crazy huh?
Sorry for the late approval of your comment, I just saw it. If I understand correctly, then yes, it sounds reasonable – magnetic card readers respond to changing magnetic fields, and current through a looped wire – even an audio signal – can certainly cause that. So, cool discovery! 🙂
Hi idogendel, I implemented your ideas in my Magspoof implementation – “RedSpoof” works quite good
I’m very interested in making this as a hobby project, and I think that I have most of the necessary knowledge about the topic, but some parts of the assembly are unclear to me, like how to load all the cards to the microcontroller and some other parts of the project. I was wondering if there was any sort of step by step guide to this project that could help me assemble it. If you do have one or are able to easily find or make one, please reply with a link to the guide.
All I have on this topic is this post, and most of it is based on Samy’s post…
igendel, are you still around I could perhaps email you a question. I’m literally stuck, could use your expertise just to figure out where I am zoned out regarding my MS V3.
I’m still around but I haven’t touched this subject since the post, so I highly doubt I can help with someone else’s product… my mail is programming AT idogendel.com
So, what exact changes did you have to make to the Magspoof code? I attempted to recreate this as you described unsuccessfully . I intend to produce a dozen or so magspoofs for a club event and simplifying the hardware like this would be great!
Well, I don’t remember by heart… but Samy’s code operates a motor driver IC (in two directions), and mine just turns a signal on/off for a transistor, so look for the part that outputs the data signals and change accordingly 🙂
Interesting, maybe we can switch to your method down the road. We’ve got a new version of the magspoof in production that has a few convenience improvements. More at [URL removed, please don’t put commercial links here, thanks].
Did you happen to notice any difference in read range when using the transistor instead of the motor driver?
[Sorry – momentary memory fail, I updated this comment!] I did not run exact experiments and measurements, and did not notice a significant difference between the versions. Both gave me a range of a few centimeters, close enough to what Sami presented, so I let it go at that.